Securing your
Environment - TacTero
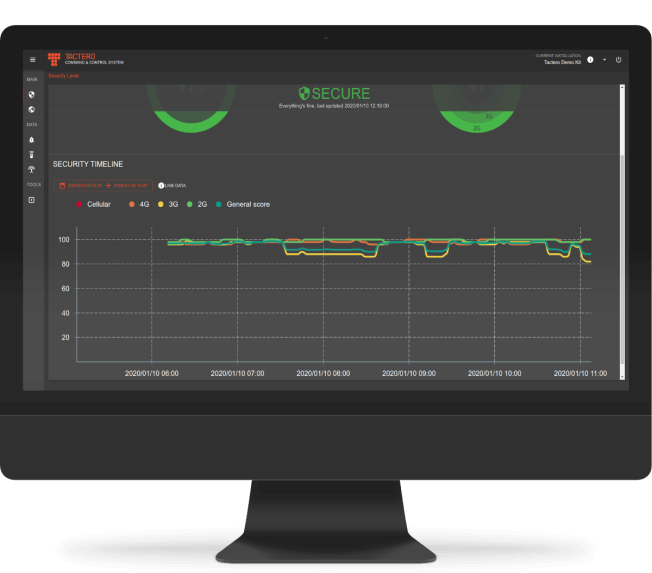
Telecommunications Security

TacTero | Feel safe in your network
Tactero defends your cellular and Wi-Fi communications from IMSI catchers, rogue access points, and similar attacks against your radio access networks.
IMSI catchers are used by advanced adversaries to intercept cellular voice, data, and SMS communications.
IMSI catchers silently downgrade encryption and other security mechanisms to locate devices, steal sensitive information, and inject malicious data onto the targeted device. Tactero is the only effective defense against these advanced attacks.
IMSI catchers are used by advanced adversaries to intercept cellular voice, data, and SMS communications.
IMSI catchers silently downgrade encryption and other security mechanisms to locate devices, steal sensitive information, and inject malicious data onto the targeted device. Tactero is the only effective defense against these advanced attacks.

Passive Features
- Rogue IMSI/Wi-Fi catcher detection – monitor radio signals and process the signals at the Tactero probes and Tactero server to detect malicious devices
- 2G/3G/4G communication decoding – focused on the most common cellular radio access technology (5G available as an optional component)
- Radio spectrum usage & abnormalities – uses software defined radio (SDR) probes to improve detection and reduce false positives
Active Features
- Cell locking & attach attempt – connect to malicious devices to catalog their activity
- Device fingerprinting – build database of IMSI/Wi-Fi catcher behavior
Optional Features
- Jamming – active methods of neutralizing rogue devices once detected
- Honeypot – active method of feeding IMSI/Wi-Fi catcher false data to thwart attackers
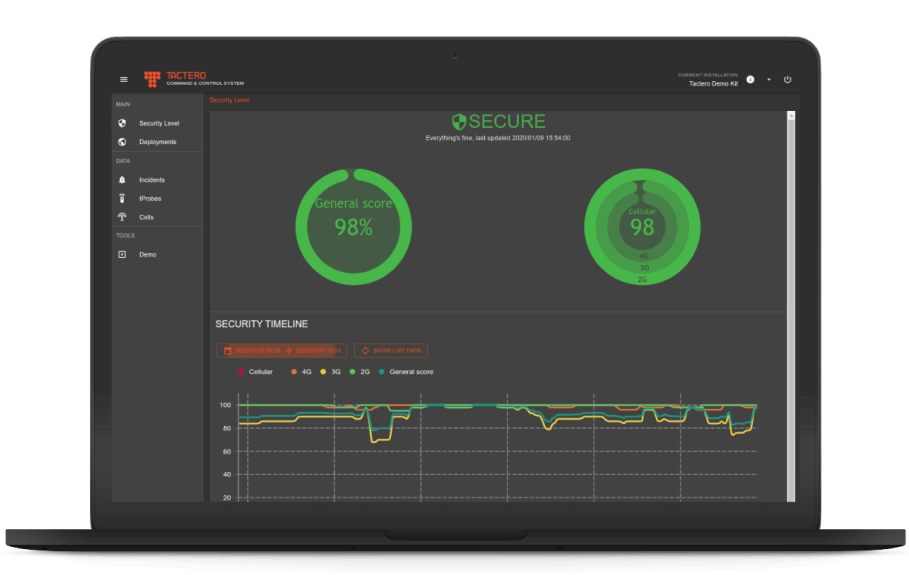
CELLULAR NETWORK DEFENSE
- Detect and fingerprint cellular base stations;
- Analyze the behavior of new and existing stations to detect malicious activity;
- Alert when malicious base stations (IMSI catchers) are detected.
- Analyze the behavior of new and existing stations to detect malicious activity;
- Alert when malicious base stations (IMSI catchers) are detected.
WI-FI NETWORK DEFENSE
- Detect rogue Wi-Fi base stations;
- Monitor Wi-Fi networks for malicious activity;
- Protect IoT devices on Wi-Fi networks;
- Inventory Wi-Fi devices in your location.
- Monitor Wi-Fi networks for malicious activity;
- Protect IoT devices on Wi-Fi networks;
- Inventory Wi-Fi devices in your location.
OPTIONAL FEATURES
- Protect Bluetooth, 5G, ZigBee, LoRa and other radio access networks;
- Integrate active countermeasures to disable detected threats;
- Integrate with your existing SOC environment.
- Integrate active countermeasures to disable detected threats;
- Integrate with your existing SOC environment.
Explore all our services

Telecommunications Security
Talk to a Forward Defense Security expert today
Is your business secure? Complete the meeting schedule form to talk with a Forward Defense Security expert about your compliance and security needs.
Get a quote