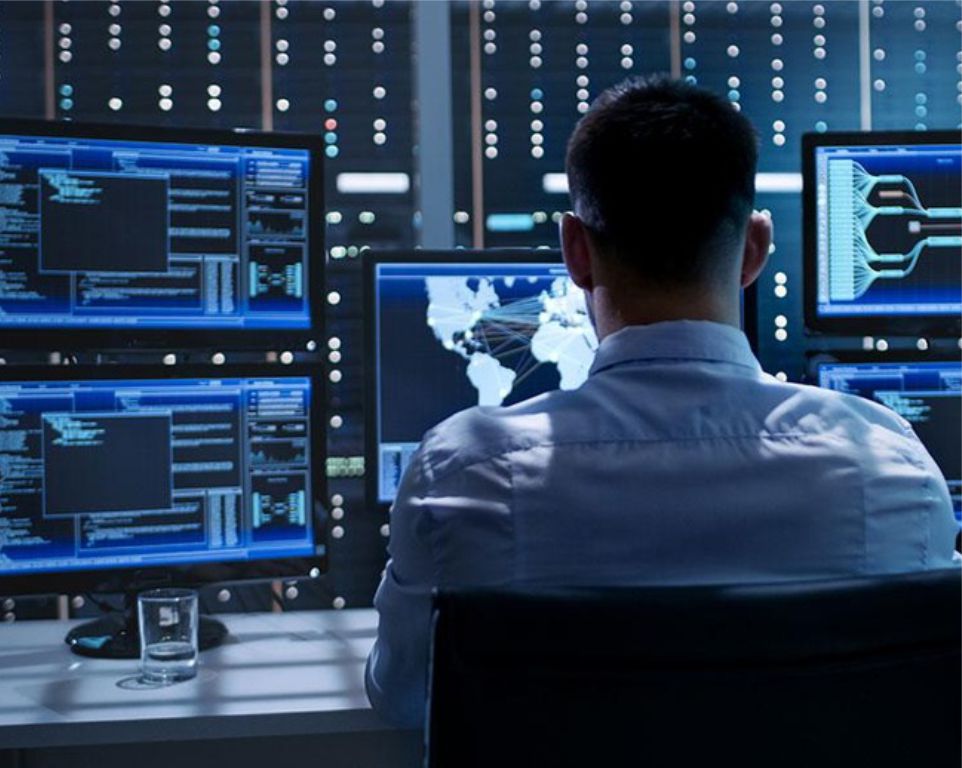
Active Cyber Defense
Proactive cyber defence means acting in anticipation to oppose an attack through cyber and cognitive domains. It represents the thermocline between purely offensive and defensive action.
Active Cyber Defense Assessment and Design
We expose your cyber enemies and eliminate them from your network by leveraging anomaly analysis, active hunting, cyber-recon by fire, and clear-and-hold missions.
Combatting criminals or organizations that are constantly battling against your network infrastructure requires you to proactively investigate, track down and, with prejudice, remove them.
Combatting criminals or organizations that are constantly battling against your network infrastructure requires you to proactively investigate, track down and, with prejudice, remove them.

Vulnerability Assessment and Penetration Testing
A staple of any network security program, vulnerability assessments (VA), supported by penetration testing (PT) to confirm findings, remain a valuable tool to identify and remediate security deficiencies in the network. Unlike adversary emulation engagements, VAPT testing is done using scans that are thorough but easy to detect, and thus would not be used by real-world adversaries.

Red Team Exercises and Adversary Emulation
Traditional vulnerability assessments and penetration tests are an important way to assess the security posture of your organization’s IT networks, looking for vulnerabilities and exposures that can be leveraged as targets of opportunity by a wide range of attackers. However, these types of assessments alone do not adequately simulate attacks from dedicated adversaries who are intent on breaching your network.
Purple team exercises
Purple team exercises provide dramatic improvements to your ability to prevent and detect cyber attacks. These exercises combine red team (offensive attack) and blue team (network defense) elements with the goal of improving your preventive and detective controls.
The result is actionable improvement to your defensive capabilities against real-world threats.
The result is actionable improvement to your defensive capabilities against real-world threats.
Threat Hunting
Search and Destroy | Hacks happen. Don’t pretend it won’t happen to you. Don’t pretend it hasn’t already.
Actively looking for indicators of compromise is a necessary part of today’s IT security practices. Passive defense has been insufficient for a decade. Perimeter defenses are not enough, and even layered defense-in-depth approaches fail eventually.
Actively looking for indicators of compromise is a necessary part of today’s IT security practices. Passive defense has been insufficient for a decade. Perimeter defenses are not enough, and even layered defense-in-depth approaches fail eventually.
Incident Response
Your network is inundated with events that may seem suspicious, but when one of those turns into a declared security incident you need fast and effective incident response to mitigate the potential damage, determine the root cause, and prevent future problems.
Our team has been conducting incident response for government and corporate clients for well over a decade.
Our team has been conducting incident response for government and corporate clients for well over a decade.

Cyber Deception
Cyber deception refers to taking steps to confuse and draw out attackers within your environment.
By placing a variety of false flags throughout your organization, adversaries can be detected when they interact with those systems while moving through and enumerating the systems in your environment.
By placing a variety of false flags throughout your organization, adversaries can be detected when they interact with those systems while moving through and enumerating the systems in your environment.
Cyber threat intelligence
Cyber threat intelligence helps you understand the world around you and the dangers that it represents to your digital assets. How exactly your organization can utilize cyber threat intelligence depends upon your overall security maturity.
Before any real value can be realized by cyber threat intelligence or other advanced defensive strategies, you must first ensure that your general IT security hygiene, including asset management and vulnerability management, are properly addressed.
Before any real value can be realized by cyber threat intelligence or other advanced defensive strategies, you must first ensure that your general IT security hygiene, including asset management and vulnerability management, are properly addressed.
Explore all our services

Telecommunications Security
Talk to a Forward Defense Security expert today
Is your business secure? Complete the meeting schedule form to talk with a Forward Defense Security expert about your compliance and security needs.
Get a quote